Dangerous toys: Anything to ed25519 (SSH Keys)
Disclaimer: I’m not a professional cryptographer or anything like that, I’ve found it interesting to dig deep into ECC and alike crypto, use at own risk and such :)
BIG NOTE: After much discussion in communities it seems like a general misunderstanding from many people where they think this is a “password to key” tool. It is not, if you use it for that purpose you’re stupid. This is for allowing you to generate more pleasant seeds for your private key, like a 64char HEX string. Rather than having to fight the keyboard typing in a base64 key when you’re already super stressed because your infrastructure is down and you’re in the middle of a disaster recovery. (Ref bellow) Wouldn’t you love enter those A’s and beg you counted right?
—–BEGIN OPENSSH PRIVATE KEY—– b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAAAMwAAAAtz
Extra note: Some awesome users at lobste.rs discovered some newbie mistakes I did way back when I coded the initial code and was in the beginning of crypto learning and I’ve afterwards patched the code and been carefully read over hunting any potential issues. Special thanks to lobsters’s user zeebo!
A couple of years back I wrote a Golang binary which took whatever it got from stdin and generated a ready to use openssh keypair (a id_ed25519 and a id_ed25519.pub with standard names). I then forgot about it, didn’t even put it into git. However back in August last year we had a case at work where
such would be perfect, so I managed to dig it back up and release it onto github for anyone to use.
This tool/toy (whatever you wanna name it) can be very practical but also extremly dangerous if used lightly without thinking about the security. It might just open your production environment to the wrong people if you don’t use good enough seeds. And just so you know, the human brain isn’t really equiped with good entropy so my adivce is to never use a key with something you just figured out of your own. Use a random strong key - the primary usage, at least from my side is backup keys that can be written down on a paper and stored offline somewhere safe.
However, I can’t stress enough how crazy bad of a idea it is to use weak keys, like the ed25519 key you get from echo hello | anything2ed25519 cause everyone can easily guess that kind of weak key. Use a dictionary and you have plenty of weak keys to test out if you’re the bad guy. So be sure to use a lot stronger seeds.
If any key from this tool should end up in anyone’s production environment, you should strictly follow the cryptocurrency guidelines about mnemonics keys. Nothing less than 24 random words, or some cryptographic strong random data of 32 bytes or more.
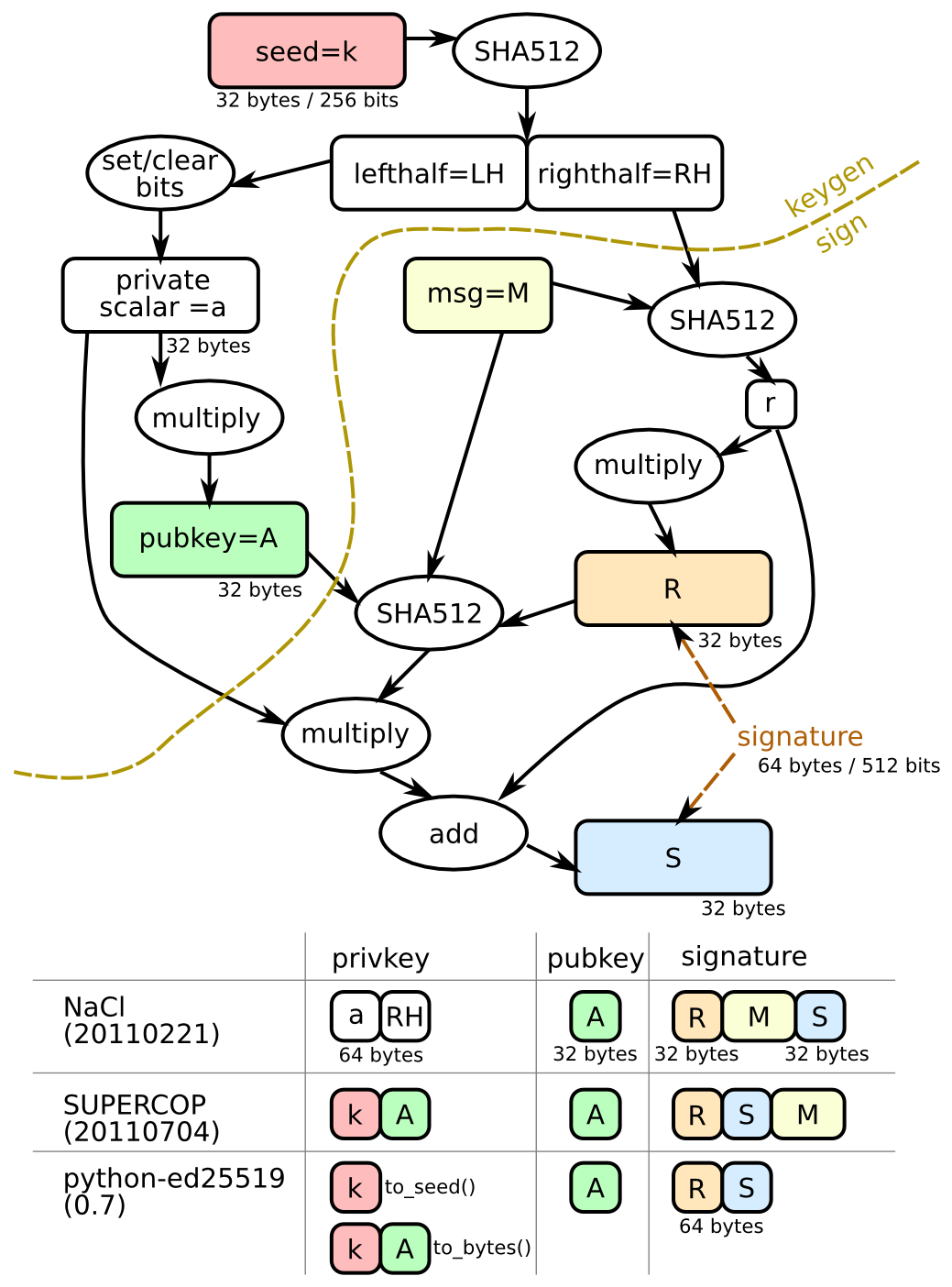
The trick is that the seed is put into a SHA256 hash, which results in a valid twisted edwards 255^19 key. So in theory you can even generate your keys from
a binary file like a jpg or dll even I wouldn’t recommend it as bigger files are hard to keep exactly the same bits over time, specially if you’re maybe
passing those files over different filesystems and operting systems and other scary stuff that might change something outside of your control and you won’t be able to recover your key.
Recommendations
If cryptography and security isn’t your strong side, you should probably skip using this tool. It will probably do more harm than good..
Demo time
In my “demo” I use just a random seed, but the way this tool works is that it would produce the exact same private and public key, given the input is exactly the same both times.
anything2ed25519 on main [?] via 🐹 v1.17.2
❯ openssl rand -base64 64 | tr -d '\n' | ./anything2ed25519-darwin-amd64.macho
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAAAMwAAAAtz
c2gtZWQyNTUxOQAAACB2LyhtKUdHZGdnpktmRSsBf2zW1/zorATpx2yPdqdSUQAA
AIiaywRCmssEQgAAAAtzc2gtZWQyNTUxOQAAACB2LyhtKUdHZGdnpktmRSsBf2zW
1/zorATpx2yPdqdSUQAAAEA0YjU5ODZiZTk4MTY2MzA4Y2NiZGMwMzU1NTVkYjc3
ZHYvKG0pR0dkZ2emS2ZFKwF/bNbX/OisBOnHbI92p1JRAAAAAAECAwQF
-----END OPENSSH PRIVATE KEY-----
ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIIteEylauQyG0WXHPv18+u7B+yBURUMVUf9+F3ogil86
anything2ed25519 on main [?] via 🐹 v1.17.2
❯ ls id_ed25519*
id_ed25519 id_ed25519.pub
Sources
The repo is found at https://github.com/mikalv/anything2ed25519